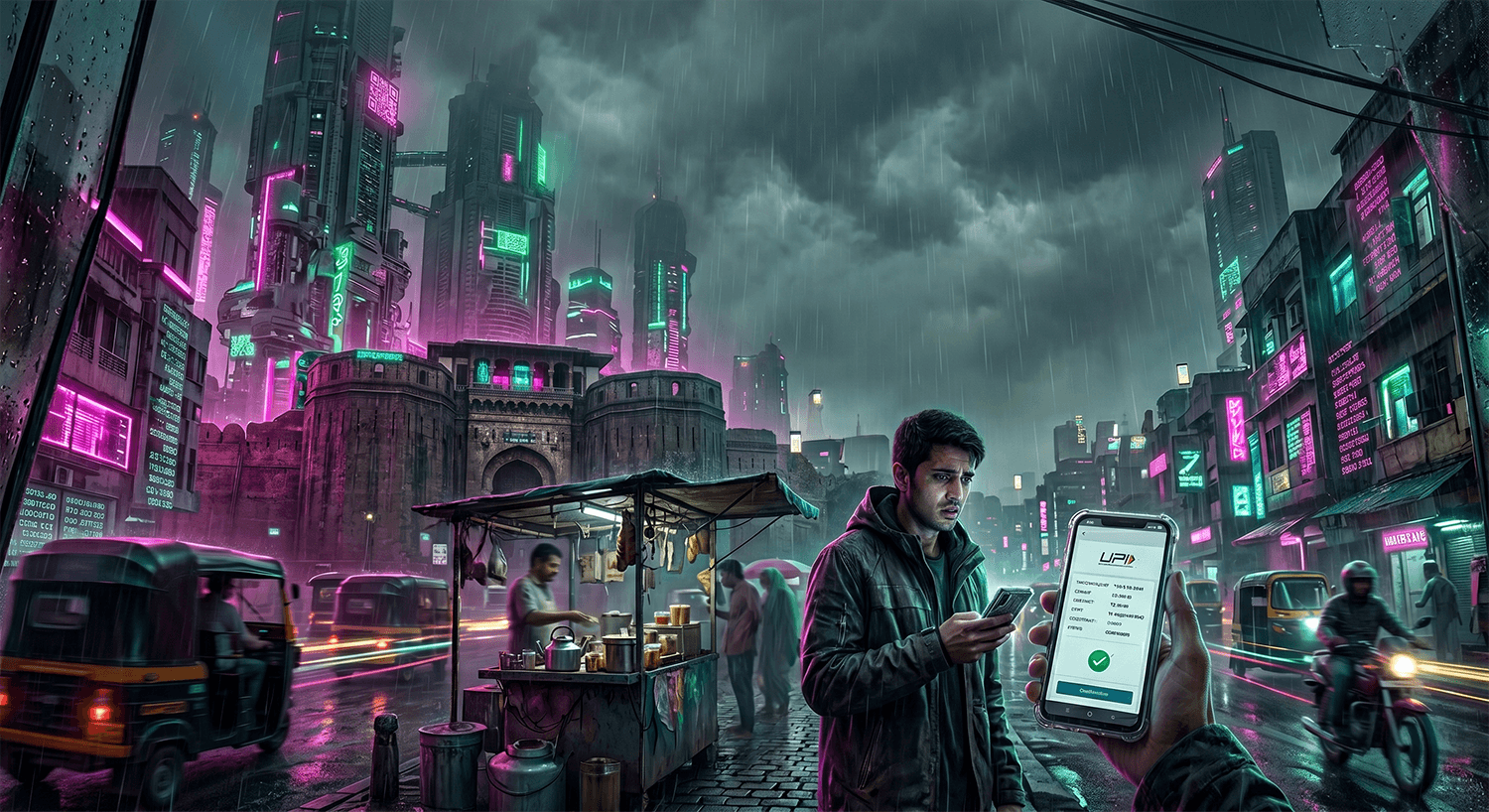
How the Payment Verification Cyber Fraud Works
Scammers operating across India and increasingly targeting US-based victims are running a sophisticated payment verification scheme that exploits trust and urgency. The scam typically begins when a fraudster contacts you via email, text message, phone call, or messaging app claiming to represent a legitimate business, government agency, or financial institution. They might say there's a problem with your account, a pending payment that needs confirmation, a refund waiting for you, or a security issue requiring immediate verification.
The attacker's goal is to convince you to make a payment, transfer money, or provide sensitive financial information under the guise of verification. They use high-pressure tactics, artificial deadlines, and official-sounding language to bypass your natural skepticism. For example, they might claim your bank account will be frozen in 24 hours unless you verify your details, or that you're eligible for a government subsidy but must pay a processing fee first. Some variants involve fake payment gateways, convincing websites that mirror legitimate services, or requests to purchase gift cards or cryptocurrency as a "temporary security measure."
Once you make the initial payment or share critical information like your bank account number, password, or social security number, the scammer has several options. They might drain your account directly, use your credentials to open new accounts in your name, or contact you again claiming there was an error and demanding additional payments. The scam often escalates: after the first successful payment, victims report being contacted repeatedly with new fabricated problems requiring additional wire transfers, ranging from $500 to over $50,000 in documented cases.
What makes these payment verification schemes particularly dangerous is that they target people across all income levels and education backgrounds. The scammers are well-organized, often operating from call centers in India and other countries, using VoIP technology to mask their location, and employing a playbook refined through thousands of attempts. They may also use publicly available information from data breaches, social media, or stolen databases to personalize their approach, making their claims seem more credible.
Red Flags to Watch For
Unexpected contact about a payment or account issue you didn't initiate: Legitimate companies rarely contact you out of the blue demanding immediate payment verification. Scammers often contact you first, which breaks the normal business pattern.
Pressure to pay immediately or face consequences like account freezing, legal action, or service cancellation: This artificial urgency is the signature of payment verification fraud. Real institutions give you time to verify claims and dispute charges.
Requests to pay via gift cards, wire transfer, cryptocurrency, or other hard-to-trace methods: Legitimate businesses accept standard payment methods and won't ask you to buy gift cards to "verify" your account.
Links or phone numbers in unexpected emails or texts that don't match the official website or number you know: Scammers create fake websites and use spoofed phone numbers. Always independently verify by calling the official number on your bill or the company's real website.
Asking you to confirm sensitive information like passwords, Social Security numbers, bank account details, or credit card numbers: Real companies already have this information. They will never ask you to provide it over email, text, or phone.
Grammar errors, unusual phrasing, or generic greetings like "Dear Customer" instead of your actual name: Many scammers operate internationally and their messages may contain language inconsistencies.
Offers that seem too good to be true, such as guaranteed refunds, free money, or subsidies you didn't apply for: If you didn't request something, you shouldn't have to pay to receive it.
Refusal to let you hang up and call back, or pressure to stay on the phone while you "verify" information: Legitimate customer service representatives understand if you want to verify their identity independently.
Real Victim Report
One Pune-based software professional reported to the Cyber Crime Cell that she received a call claiming to be from her bank's fraud department, warning that unauthorized transactions were pending on her account. The caller spoke fluent English, provided her partial account number, and created such a convincing sense of urgency that she agreed to verify her identity by making a test payment of ₹50,000 (approximately $600 USD) to a provided account. Only after the transfer did she realize the "verification" made no sense, and by then the money was gone, traced to a shell account that was quickly emptied.
What To Do If You've Been Targeted
Stop all contact immediately. Do not respond to further messages, emails, or calls from the sender. Block their number and mark emails as spam. Do not engage further even to argue or ask questions, as this can be used to refine their social engineering approach.
Do not send any additional money or information. If you've already transferred funds, it may be too late to recover them, but sending more money only deepens your loss. Scammers often use "recovery fee" schemes to compound the original theft.
Report the incident to the FTC immediately at reportfraud.ftc.gov. The Federal Trade Commission maintains a database of fraud complaints that helps identify patterns and supports law enforcement investigations. Provide all details: date, time, method of contact, exact language used, money amount, and account details if applicable.
File a complaint with the FBI's Internet Crime Complaint Center (IC3) at ic3.gov. IC3 coordinates with international law enforcement and tracks organized cyber fraud rings. Your report may be linked with others targeting the same organization, strengthening the investigation.
Contact your bank or financial institution immediately if you transferred money, gave account details, or shared payment information. Ask them to freeze the account, reverse transactions if possible, and monitor for unauthorized activity. Report the fraudulent recipient account number so the bank can flag it.
Place a fraud alert with the three major credit bureaus (Equifax, Experian, and TransUnion) by calling 1-888-5-OPTOUT or visiting their websites. A fraud alert makes it harder for scammers to open new accounts in your name. Consider a credit freeze if sensitive personal information was compromised.
Monitor your accounts and credit reports closely for the next 12 months. Check your credit report annually at annualcreditreport.com for unauthorized accounts or inquiries. If significant personal data was exposed, consider identity protection services like Aura (aura.com/recentscam) to provide ongoing monitoring and alerts for suspicious activity.
How To Protect Yourself Going Forward
Always verify independently before responding to payment requests. If you receive a call, email, or text claiming to be from your bank, government agency, or a service provider, hang up immediately and call the official number listed on your statement, bill, or the organization's official website. Never use contact information provided in the unsolicited message, as scammers often spoof legitimate numbers.
Never provide sensitive information in response to unsolicited contact. This includes passwords, Social Security numbers, bank account numbers, credit card details, dates of birth, or security questions. Real organizations will not request this information via email, text, or unexpected phone calls. If you're unsure, ask for the caller's name and department, end the call, and contact the organization directly using a number you verify independently.
Be skeptical of payment methods that are hard to reverse, such as wire transfers, gift cards, or cryptocurrency. These are favorite tools of scammers because once the money is sent, it's nearly impossible to recover. Legitimate businesses accept credit cards, debit cards, and checks, which offer protections. If a company insists on untraceable payment methods, it's almost certainly a scam.
Enable two-factor authentication (2FA) on all important accounts like email, banking, and social media. This means that even if a scammer obtains your password, they cannot access your account without a second verification step like a code from your phone. This single step blocks the majority of account takeover fraud.
Frequently Asked Questions
I gave a scammer my bank account number. What should I do immediately? ▼
Can I get my money back if I sent it via wire transfer or gift card? ▼
How can I tell if a phone number or email claiming to be from my bank is real? ▼
Written By
Maya covers consumer fraud and digital safety. Her work has focused on telecom scams, AI-driven impersonation, and the people behind the numbers.