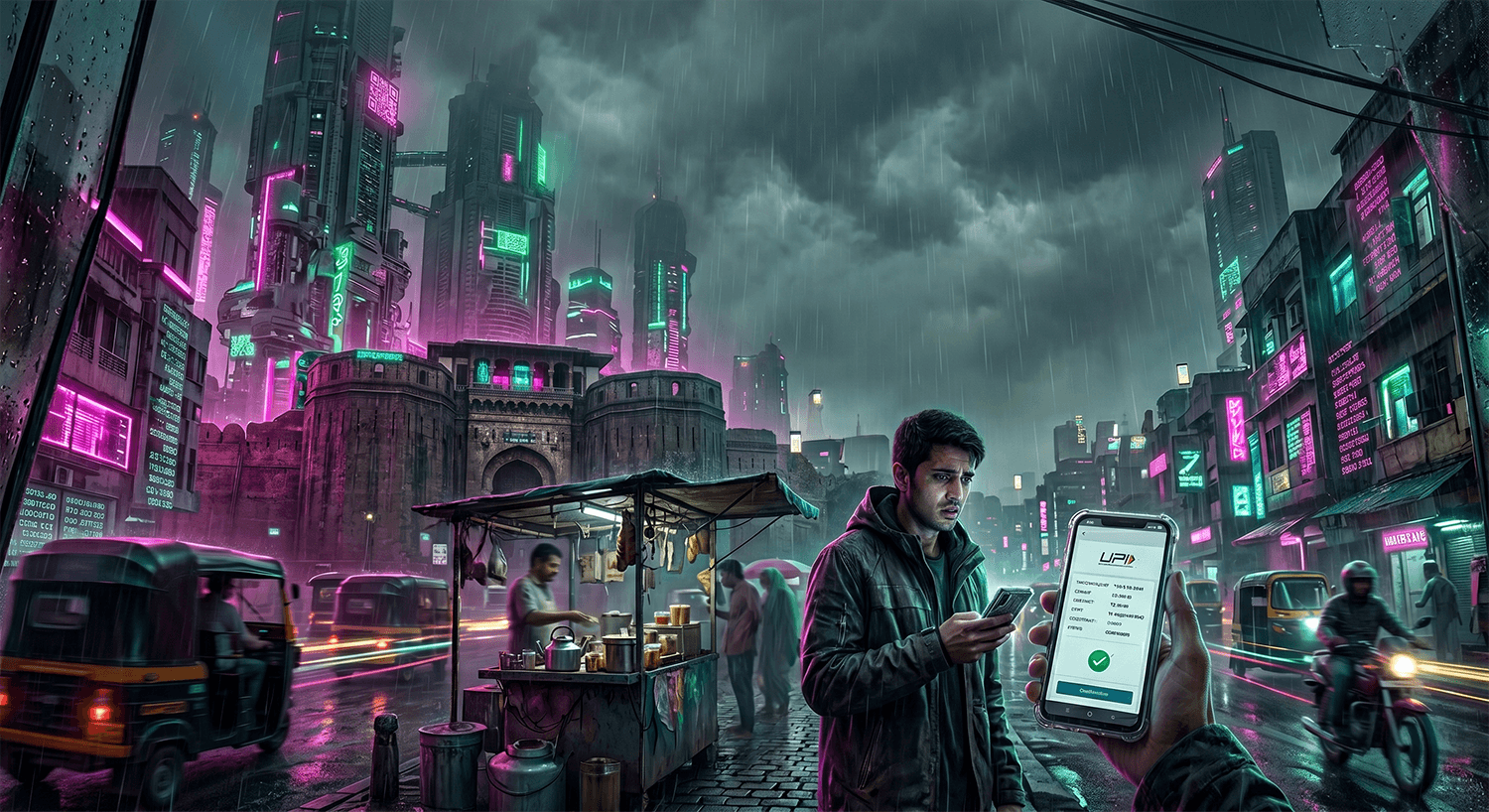
How the Telecom Impersonation Scam Works
The telecom impersonation scam is a carefully orchestrated fraud that exploits the trust most people place in their phone and internet service providers. The scam typically begins with an unsolicited phone call, text message, or email appearing to come from your cellular carrier or Internet Service Provider. The scammer uses caller ID spoofing technology to make the call appear to originate from your actual service provider's official customer service line, complete with a legitimate-looking number and company name on your screen.
Once they have your attention, the scammer claims there is a serious problem with your account. They might say your service is about to be suspended due to unpaid bills, that there has been fraudulent activity detected, that your account has been compromised, or that you qualify for a special upgrade or refund. The language is urgent and official, often peppered with technical jargon designed to sound authentic. The scammer might reference your account number (which they obtained through data breaches or public records) or ask you to verify personal information to "confirm your identity" before they can help.
The real trap comes next. The scammer directs you to take immediate action to "resolve" the problem. They might instruct you to purchase gift cards (Google Play, iTunes, Amazon, or other retailers), cryptocurrency, or wire transfer funds to a specific account. Some variations involve convincing you to authorize remote access to your computer or phone, where they then gain control of your banking apps, two-factor authentication codes, and other sensitive data. The scammer maintains the illusion by keeping you on the phone throughout the process, offering reassurance and walking you through each step. Once the money is sent or remote access is granted, the scammer disappears, and victims realize too late that their service provider would never demand payment via gift cards or cryptocurrency.
Red Flags to Watch For
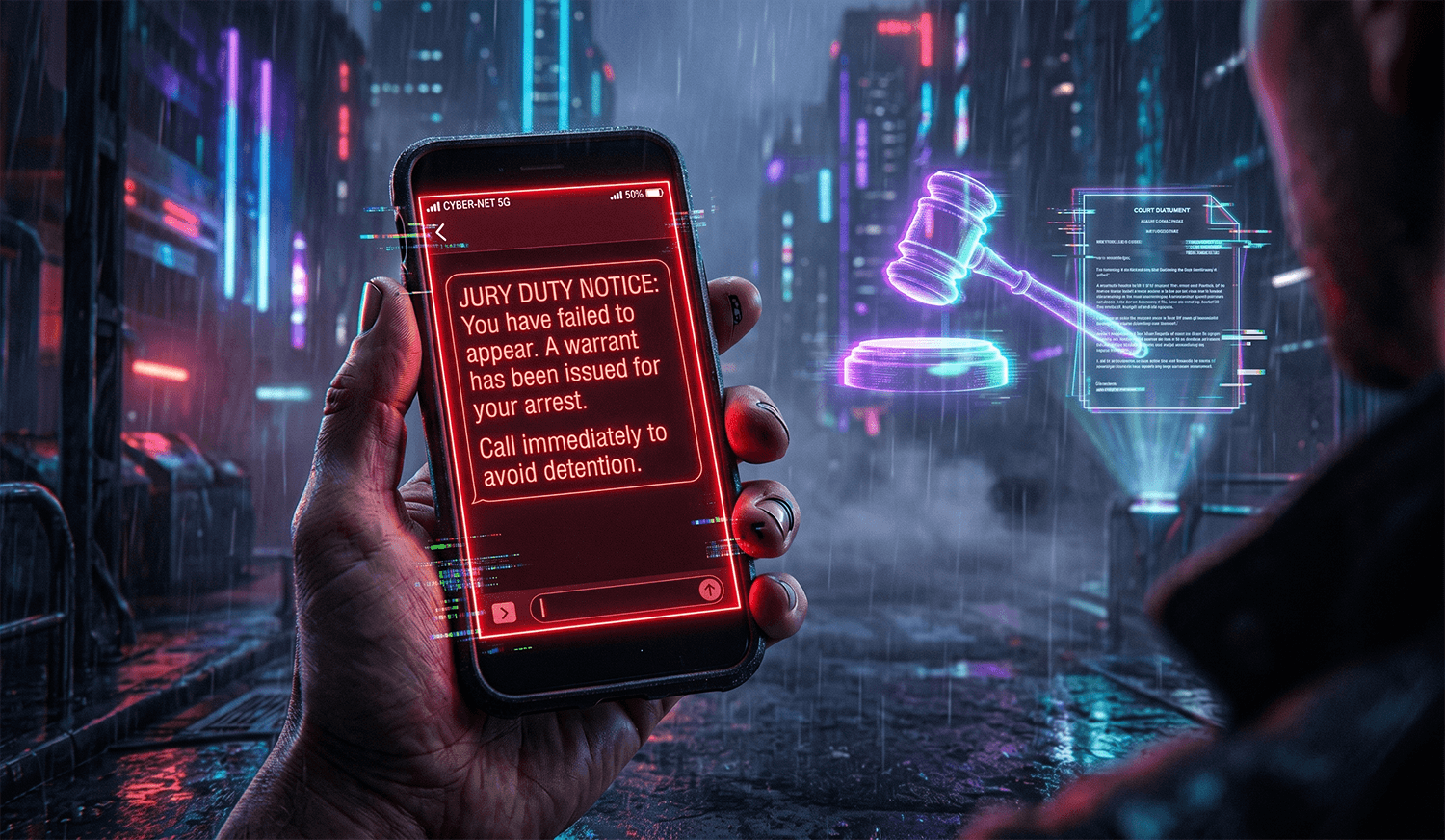
- Your service provider calls claiming you need to act immediately or your service will be cut off, or that you are owed a refund and need to provide payment information to claim it. This is the hallmark of telecom scams. Real service providers do not demand immediate action via phone call for account issues.
- Your caller ID shows your service provider's name and a local or familiar phone number, yet when you call that number back independently, customer service has no record of the call.
- The caller asks you to purchase gift cards, wire money, or send cryptocurrency to "resolve" the issue. Legitimate carriers never ask for payment through these methods.
- You are told to avoid calling the customer service number on your bill or your official service provider website, with claims that "those lines are compromised" or "our system is down."
- The caller requests remote access to your computer, phone, or asks you to install an app to "verify" your account or "show you the problem."
- You are asked to provide or confirm sensitive information like your Social Security number, account PIN, online banking username and password, or credit card details over the phone.
- The conversation becomes evasive or nonsensical when you ask specific questions about your account, billing address, or service history that a real representative should easily answer.
- You receive follow-up messages via text or email with suspicious links claiming to be from your service provider, especially links requesting you to log in or update your payment method.
Real Victim Report
One retired educator in a mid-sized city reported to the FTC that she received a call appearing to come from her cellular provider claiming fraudulent activity had been detected on her account and that she needed to act within 30 minutes to prevent service suspension and financial liability. Convinced of the legitimacy by the caller's detailed knowledge of her plan and account number, she followed the scammer's instructions to purchase and load gift cards, ultimately losing over $100,000 across multiple transactions over several weeks. By the time she realized the scam, the funds had been transferred out of the gift card accounts, and her service provider confirmed they had never contacted her.
What To Do If You've Been Targeted
Stop all contact immediately. Hang up the phone or stop responding to messages. Do not continue the conversation, answer additional questions, or follow any further instructions from the caller.
Do not send any more money or provide additional personal information. If you have already sent money via gift cards or wire transfer, contact those platforms immediately (Google Play, Apple, Amazon, Western Union, etc.) and explain that you were a victim of fraud. Some providers can freeze or reverse transactions if you act quickly enough.
Report the scam to the FTC at reportfraud.ftc.gov. This creates an official record and helps law enforcement identify patterns. Be as detailed as possible: the date and time of the call, the phone number displayed, the exact language used, and any money lost.
File a complaint with the FBI's Internet Crime Complaint Center at ic3.gov. This is particularly important if large amounts of money or sensitive data were involved. The IC3 maintains a national database of cyber fraud reports.
Contact your actual service provider's official customer service line (use the number on your bill, not any number the scammer provided) and inform them of the scam. Ask them to review your account for any unauthorized changes, new devices added, or suspicious activity. They may be able to reverse certain charges if you report quickly.
Place a fraud alert with the major credit bureaus (Equifax, Experian, and TransUnion) by visiting IdentityTheft.gov. This makes it harder for scammers to open new accounts in your name. If you shared sensitive personal information like your Social Security number, consider freezing your credit as well.
If you granted remote access to your devices, change all of your passwords immediately from a clean device (not the one the scammer accessed). This includes email, banking, social media, and your service provider accounts. If you provided banking credentials, contact your bank right away and monitor your accounts closely for unauthorized transactions.
How To Protect Yourself Going Forward
Remember that legitimate service providers will never contact you unexpectedly demanding immediate payment, gift cards, or cryptocurrency. Your carrier's official customer service is always available through the number on your bill, their website, or by visiting a physical store location. If you receive a suspicious call from your service provider, hang up and call the official number yourself to verify whether the issue is real.
Enable two-factor authentication on all of your accounts, especially email and banking. This prevents scammers from accessing your accounts even if they obtain your password. Be cautious about which personal information you share publicly on social media; details like your birthday, hometown, employer, and phone number can all be used by scammers to make their calls sound more convincing.
Consider using a service like Aura (aura.com/recentscam) that monitors your personal information across the dark web and alerts you if your data has been compromised in a breach. Many scammers rely on stolen data to sound authentic during their calls. Knowing whether your information is already compromised can help you take preventative steps. Additionally, set up call filtering on your phone to block spam and spoofed numbers; most carriers offer this as a free or low-cost feature.