How the Credit Card Cloning Scam Works
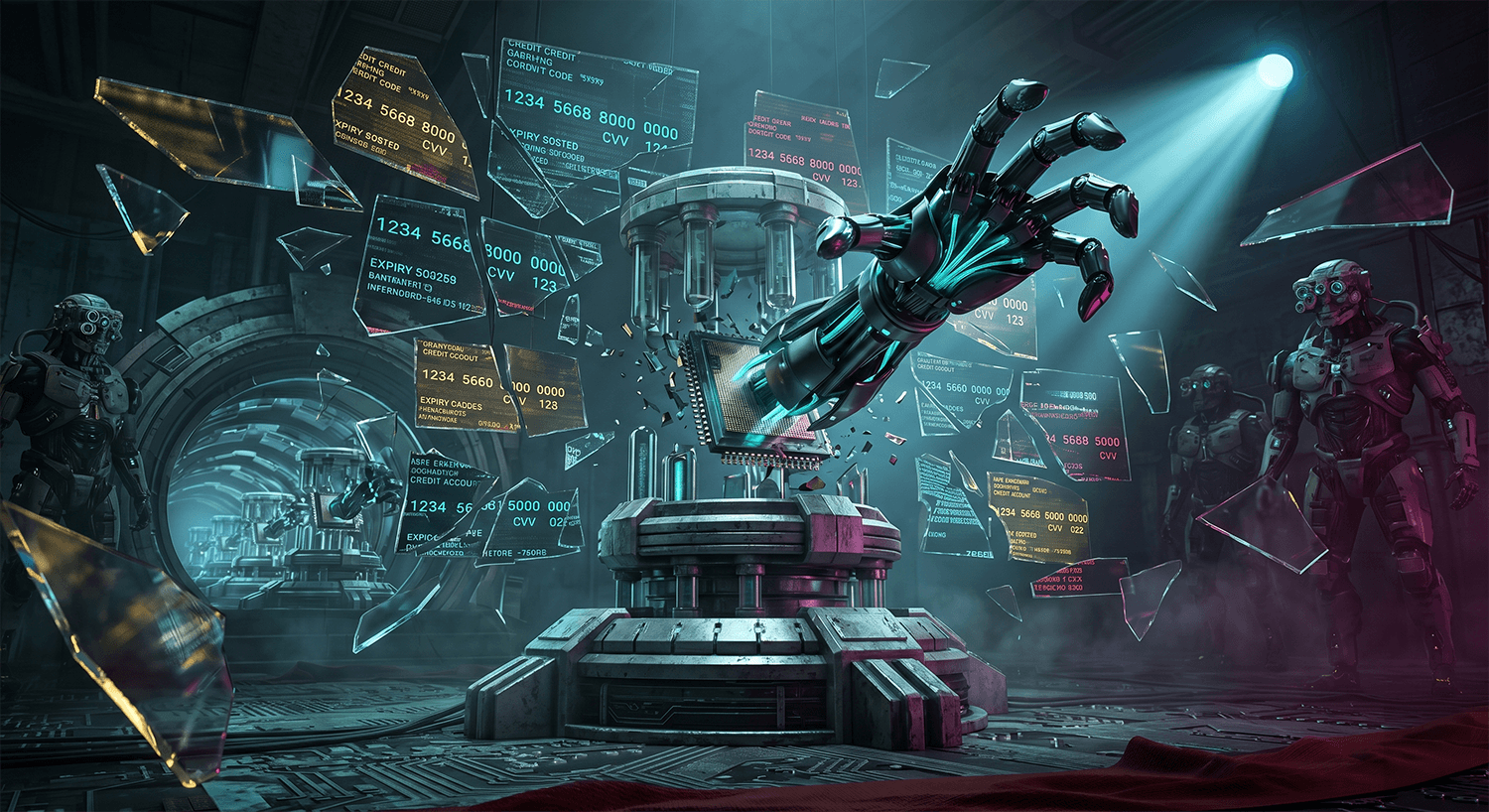
Credit card cloning represents one of the most damaging forms of identity theft operating in 2026, and it doesn't discriminate between ordinary citizens and well-known public figures. The scam begins when criminals obtain your card information through various methods: skimming devices placed on ATM machines, data breaches at retailers, phishing emails that trick you into entering your details, or through compromised online shopping sites. Once they have your card number, expiration date, and CVV, they clone the card by creating a duplicate with the same information encoded onto a blank card or by using the data for online purchases.
The fraudsters typically work in organized rings, with some team members handling the theft of information while others manage the actual use of the cloned cards. They may test the card with small purchases first, amounts under fifty dollars, to verify the card is active and the victim hasn't yet noticed suspicious activity. Within hours or days, they escalate to larger purchases, often targeting electronics, gift cards, or items they can quickly resell. The beauty of this scam from the criminal's perspective is that it creates distance between the theft and the victim: the victim doesn't realize their card has been compromised until they review their statement or receive a fraud alert from their bank.
What makes this scam particularly insidious is that it exploits the trust people place in legitimate payment systems. Victims often don't realize they've been targeted until dozens or hundreds of dollars have already been spent. In high-profile cases similar to those reported by major Indian media outlets, victims discovered unauthorized charges appearing across multiple merchants, sometimes in different geographic locations within impossible timeframes. The scammers use various tactics to stay ahead of detection, including making purchases at different times of day, at different retailers, and sometimes in different cities or states to avoid triggering fraud detection systems too quickly.
Red Flags to Watch For
You receive a text or call from your bank asking you to verify recent charges you don't recognize, but the caller has your full card number and personal details already, which should only happen if your card was truly compromised. This is often a sign that fraud has already occurred.
Unfamiliar charges appear on your statement for purchases at retailers you don't use or in locations you haven't traveled to recently.
You notice small test charges of one to five dollars appearing multiple times at the same merchant, followed by larger purchases.
Your card is still physically in your possession, yet charges are appearing from online retailers or far-away locations, indicating someone has cloned your card information.
You receive order confirmation emails for items you never purchased, with shipping addresses you don't recognize.
Your credit card company calls you multiple times in a short period asking about different transactions, suggesting multiple fraudulent attempts.
You discover that a duplicate card was activated or ordered under your name without your authorization.
Merchants reject your card during legitimate transactions, but you later see successful charges from fraudsters, indicating the card was compromised and flagged for fraud early on.
Real Victim Report
One Mumbai, Maharashtra resident reported to the Federal Trade Commission that he discovered over fourteen thousand rupees in unauthorized charges on his credit card statement, including purchases at electronics retailers he'd never visited and online payments to services he didn't use. The victim didn't notice the fraud immediately because the scammers had spread charges across multiple days and merchants, staying just below the threshold that typically triggers immediate fraud alerts from the bank. By the time he reviewed his detailed statement two weeks after the fraudulent activity began, the criminals had made approximately twenty-three separate transactions, and the card issuer informed him that the card data had likely been cloned at a point-of-sale terminal he'd used at a popular shopping destination.
What To Do If You've Been Targeted
Stop all communication with anyone who contacted you about your card if they seem suspicious, and do not provide additional information. Call your bank directly using the number on the back of your card or their official website, not a number provided by a caller or text message.
Do not pay any of the disputed charges yourself. Your bank is required by federal law to investigate unauthorized charges and reverse them if fraud is confirmed.
Report the fraud to the Federal Trade Commission immediately at reportfraud.ftc.gov. The FTC maintains a database of all fraud reports and provides valuable resources for identity theft recovery.
File a complaint with the FBI's Internet Crime Complaint Center at ic3.gov, especially if the fraud involved interstate commerce or online retailers.
Contact your bank and request that they issue you a new card with a new account number. Ask them about adding fraud alerts or security monitoring to your account.
Place a fraud alert on your credit file by contacting one of the three major credit bureaus (Equifax, Experian, or TransUnion). A fraud alert notifies lenders to verify your identity before opening new accounts in your name.
If you believe your personal information beyond just your card number has been compromised, consider enrolling in identity theft protection services like Aura at aura.com/recentscam, which monitors your credit, financial accounts, and personal data for suspicious activity.
How To Protect Yourself Going Forward
Regularly review your bank and credit card statements every week, not just monthly. Most fraud is caught within the first week if victims are actively monitoring their accounts. Set up transaction alerts on your credit card so you receive notifications of all charges over a certain amount (like twenty-five dollars) or any charges from specific merchant categories you rarely use.
Be cautious about where you use your physical card. Inspect ATM machines before inserting your card and cover the keypad when entering your PIN. When eating at restaurants or making retail purchases, try to keep your card in sight when possible. Consider using virtual card numbers or digital payment methods like mobile wallets whenever available, as these provide additional layers of security compared to physical card swiping.
Don't provide your full credit card information via email, phone, or text message unless you initiated the contact and confirmed you're speaking with a verified representative of your bank or a legitimate merchant. Legitimate companies will never ask for your CVV via email or phone. Use chip readers rather than magnetic stripe readers when available, as chip technology is more difficult for criminals to clone.
Frequently Asked Questions
How do criminals get my credit card information if I always keep my card in my wallet? ▼
If my card was cloned, am I responsible for paying those fraudulent charges? ▼
How long does it take for a bank to investigate fraud and refund my money? ▼
Written By
Our editorial team aggregates and verifies scam reports from threat-intelligence feeds (URLhaus, OpenPhish, PhishTank) and U.S. government complaint data (FTC, FCC), plus community submissions. See our methodology for how every record and article is sourced and reviewed. Read our methodology →
.jpg)